Breaches are still costly, with recent reports putting the average incident in the multimillion range, and attackers increasingly using stolen credentials and unmanaged devices to “log in” rather than break in. For mid-sized organisations with lean IT teams, that shift turns small control gaps into business risk. Zero Trust offers a practical way forward by treating every user, device and app as untrusted until verified, every time.
What Zero Trust Is, and What it Means For Your Business
Zero Trust is a security approach that never assumes trust by default. Every user, device and app must be verified each time it seeks access. The UK’s NCSC (National Cyber Security Centre) frames it as designing for continuous verification, least privilege and strong segmentation to reduce the blast radius when something goes wrong. For mid-sized organisations, that translates into fewer successful logins by attackers, smaller incidents when they occur and faster investigations.
Credentials Are Still the Easiest Way In
Attackers increasingly log in rather than break in. Microsoft observes that over 99.9% of compromised accounts did not have MFA enabled, which makes password reuse and phishing highly effective. Enforcing MFA and checking context at sign-in is one of the fastest risk reductions available. Turn on MFA for all users and admins, including SaaS and VPN. Add conditional access so authentication also checks device health, user risk and location. For smaller businesses, these steps are low-cost, quick to deploy and significantly reduce the chances of becoming an easy target.
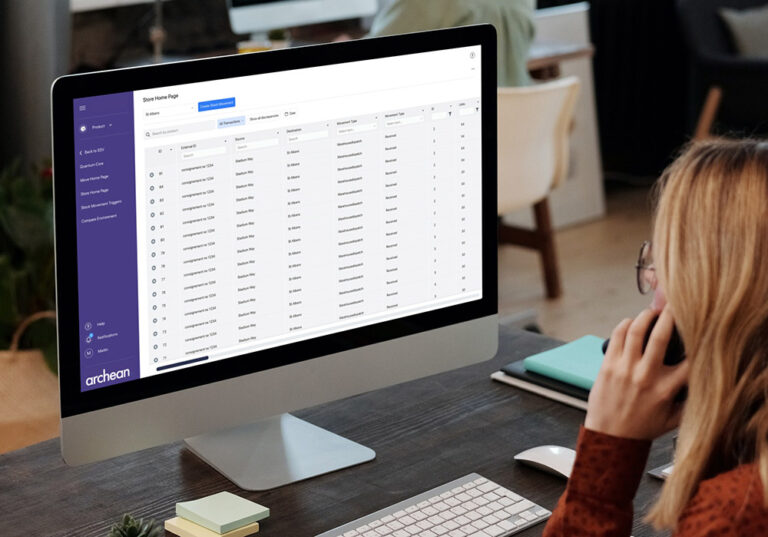
SaaS Sprawl and Shadow IT Create Blind Spots
Teams adopt new tools quickly, but unmanaged SaaS expands both risk and spend. Unapproved apps often bypass security controls, making it harder to track where sensitive data lives. Without oversight, even well-meaning teams can introduce serious vulnerabilities. Centralise identity and access management to bring SaaS under control. Inventory every app and integration, apply least-privilege access and retire duplicate or ungoverned tools. For mid-sized businesses, this not only reduces security exposure but also cuts unnecessary licensing costs.
Flat Networks Magnify the Blast Radius
Once inside, attackers thrive in environments with broad, persistent privileges and limited segmentation. A single compromised account can move laterally across systems if networks are flat and roles are not well defined. Segment high-value systems and restrict east-west traffic. Map roles to access, time-bound elevated privileges and remove dormant accounts quickly. This approach contains incidents before they escalate and keeps disruption, and costs, to a minimum for growing businesses.
Unmanaged or Outdated Devices Widen the Attack Surface
Remote and frontline devices often miss patches or controls, and a single unhealthy endpoint can become the weakest link. An outdated laptop in a branch or a personal device without proper checks can quickly undermine security. Zero Trust expects every device to prove it is healthy before access is granted. Use unified endpoint management to keep all devices visible, encrypted and up to date. Automate patching and block access from devices that fail compliance checks. This means less firefighting for IT teams and greater assurance that every device connecting to the network is secure.
Zero Trust as a Path to Secure Business
Zero Trust is not a single product or one-time project. It is a practical way of operating that reduces risk by verifying every user, device and app. For mid-sized businesses, the advantage is clear: stronger protection against common threats, fewer disruptions when incidents occur and a security model that scales as you grow. By focusing on simple, high-impact steps like MFA, device compliance, SaaS governance and network segmentation, you can make measurable improvements without overwhelming your IT team.
At Retail Assist, we help organisations put these practices into action with clear roadmaps and ongoing support. If you want to strengthen security while keeping your business agile, now is the time to start.
Talk to us